Implementing Single Sign-On (SSO) for Cisco Umbrella is a critical step toward strengthening identity-based security and streamlining user access across your organization. As cyber threats become more sophisticated in 2026, securing DNS-layer protection with a centralized authentication system is no longer optional—it is essential. This comprehensive guide walks you through the step-by-step configuration of Cisco Umbrella SSO to ensure secure, seamless, and compliant access management.
TL;DR: Configuring Cisco Umbrella SSO enhances security by centralizing user authentication through your Identity Provider (IdP). The process involves preparing your IdP, enabling SAML in Umbrella, exchanging metadata, configuring claims, and testing authentication flows. Proper configuration reduces password fatigue, strengthens access controls, and improves audit visibility. Follow each step carefully to avoid authentication failures or policy mismatches.
Why Configure SSO for Cisco Umbrella?
Cisco Umbrella provides DNS-layer security, secure web gateway features, cloud app discovery, and firewall capabilities. However, without integrated SSO, user authentication and policy enforcement can become fragmented and vulnerable.
By enabling SSO, organizations gain:
- Centralized identity management through one trusted Identity Provider
- Stronger access controls with MFA enforcement
- Reduced password fatigue for end users
- Improved audit logging and compliance reporting
- Faster user provisioning and deprovisioning
In 2026, modern enterprises typically integrate Cisco Umbrella with identity platforms such as:
- Microsoft Entra ID (formerly Azure AD)
- Okta
- Ping Identity
- Google Workspace
- ADFS
Prerequisites Before You Begin
Before starting configuration, ensure the following requirements are met:
- Administrator access to Cisco Umbrella dashboard
- Administrator privileges in your chosen Identity Provider
- SAML 2.0 capable IdP
- Accurate user directory synchronization
- Time synchronization across systems (NTP configured)
Important: Time drift between Umbrella and your IdP can cause SAML authentication failures.
Step 1: Prepare Your Identity Provider (IdP)
The first stage is configuring a new SAML application inside your Identity Provider.
General IdP Configuration Steps
- Create a new SAML 2.0 application.
- Name the application (e.g., “Cisco Umbrella SSO”).
- Configure the Assertion Consumer Service (ACS) URL using Cisco Umbrella’s SAML endpoint.
- Set the Entity ID provided by Umbrella.
- Enable signed SAML assertions.
- Choose SHA-256 as the signing algorithm.
The exact interface varies by IdP, but these foundational steps remain consistent.
Required SAML Attributes
Configure attribute mappings as follows:
- Email → user.email
- First Name → user.givenname
- Last Name → user.surname
- Unique Identifier → NameID (Email format)
Inconsistent attribute mapping is one of the most common causes of access errors.
Step 2: Enable SAML in Cisco Umbrella
Once your IdP app is ready, you must enable SAML within the Umbrella dashboard.
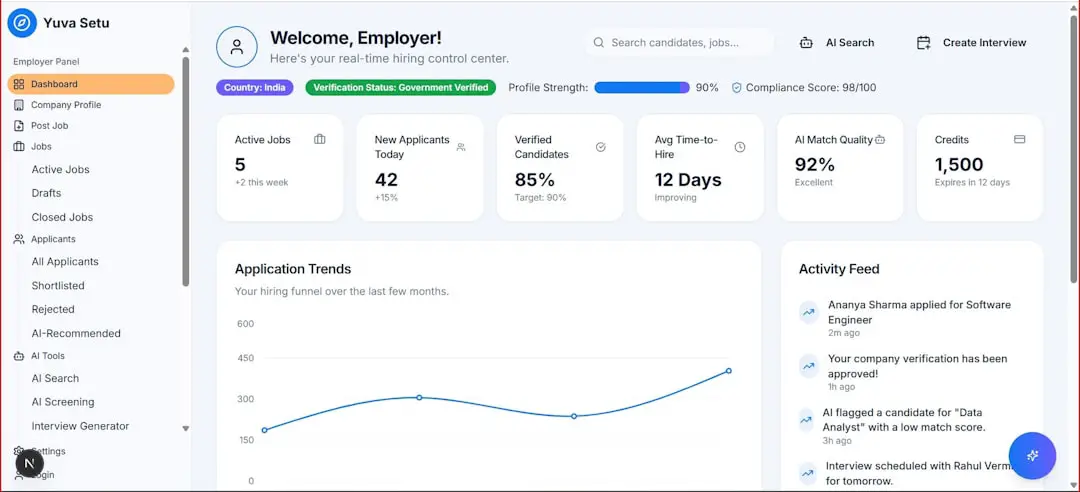
Image not found in postmetaHow to Enable SSO in Umbrella
- Log in to the Cisco Umbrella Admin Portal.
- Navigate to Admin > Authentication.
- Select Single Sign-On.
- Choose SAML as your authentication method.
- Download the Umbrella metadata file.
This metadata file must be uploaded into your Identity Provider configuration.
Step 3: Exchange Metadata Between Systems
SSO depends on a secure trust relationship between Cisco Umbrella and your IdP. This trust is established through metadata exchange.
Upload Umbrella Metadata to the IdP
- Import the Umbrella XML metadata file into your SAML application.
- Verify ACS URL auto-populates correctly.
- Confirm Entity ID accuracy.
Upload IdP Metadata to Cisco Umbrella
- Download IdP metadata file.
- Return to Umbrella SSO settings.
- Upload the IdP metadata XML file.
- Save configuration.
This step completes the cryptographic trust loop.
Step 4: Configure Access Policies in Umbrella
Authentication alone is not sufficient. Proper access control ensures secure resource enforcement.

Best Practices for Policy Mapping
- Map policies to user groups synchronized from your IdP.
- Apply stricter DNS filtering for privileged accounts.
- Enable logging and reporting for security teams.
- Configure MFA enforcement within the IdP.
Tip: Avoid overly broad group assignments. Least-privilege access should guide your configuration.
Step 5: Test the SSO Configuration
Testing ensures the configuration works correctly before full deployment.
Recommended Test Plan
- Use a non-administrative test account.
- Log out of both Umbrella and IdP sessions.
- Attempt login via Umbrella dashboard.
- Confirm redirection to IdP.
- Authenticate and verify redirect back to Umbrella.
- Validate correct policy application.
Common Issues and Solutions
- SAML response invalid: Check certificate signature and expiration date.
- User not authorized: Verify group membership mapping.
- Clock skew errors: Synchronize NTP settings.
- Incorrect NameID: Ensure email format consistency.
Audit logs inside both Umbrella and your IdP provide valuable troubleshooting insights.
Security Enhancements for 2026 Deployments
Modern security frameworks extend beyond basic SSO. Consider implementing:
Multi-Factor Authentication (MFA)
Require MFA for all administrative roles and high-risk logins.
Conditional Access Policies
- Restrict login by geographic location
- Enforce device compliance checks
- Require risk-based authentication evaluation
Certificate Rotation Policy
Establish a reminder process to rotate SAML certificates before expiration.
Zero Trust Integration
Combine Umbrella SSO with:
- Secure Access Service Edge architecture
- Endpoint posture validation
- Network segmentation strategies
SSO becomes a foundational identity pillar in a Zero Trust framework.
Comparison of Popular Identity Providers for Cisco Umbrella SSO
| Identity Provider | Ease of Setup | Advanced Security Features | Enterprise Scalability | Best For |
|---|---|---|---|---|
| Microsoft Entra ID | High | Conditional Access, Risk Based Policies | Excellent | Microsoft centric enterprises |
| Okta | High | Adaptive MFA, Lifecycle automation | Excellent | Cloud first organizations |
| Ping Identity | Moderate | Advanced federation controls | Very High | Complex enterprise environments |
| Google Workspace | Moderate | Built in MFA, Context aware access | High | Google ecosystem users |
| ADFS | Complex | On premises control | Moderate | Legacy infrastructure environments |
Choosing the right IdP depends on your organizational infrastructure and security maturity.
Maintenance and Ongoing Monitoring
SSO configurations are not static. Ongoing governance is critical.
Monthly Review Checklist
- Review failed login attempts
- Audit privileged account activity
- Validate certificate validity
- Confirm correct group synchronization
- Test fallback authentication procedures
Security posture deteriorates without consistent oversight.
Final Thoughts
Configuring Cisco Umbrella SSO in 2026 requires more than basic integration—it demands a security-first mindset. Properly implemented, SSO strengthens authentication, reduces operational complexity, and supports compliance initiatives. Incorrectly configured, however, it can introduce access failures or security gaps.
By carefully preparing your Identity Provider, establishing secure SAML trust, mapping attributes correctly, and validating policies, you build a dependable authentication framework that enhances DNS-layer security.
Organizations that treat identity as the core of cybersecurity will position themselves strongly against evolving threats. Cisco Umbrella SSO, when integrated with modern identity protections, becomes a powerful pillar in a broader Zero Trust architecture.
Secure configuration today prevents breach response tomorrow.